You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
Encryption continues to be a cornerstone of digital security, yet recent developments and regulatory pushes have thrust this issue back into public discourse. Governments worldwide are advocating for increased access to encrypted communications, citing reasons such as national security, cybercrime concerns, and child protection. Meanwhile, technology companies remain firm in their commitment to robust encryption, warning that its dilution could jeopardize user privacy, economic stability, and the overall integrity of digital platforms.
Although this conflict is not new, the current landscape, characterized by heightened urgency and greater international collaboration, has intensified the discussion. Both sides claim to act in the public's interest, yet their goals remain in stark opposition to one another.
This article delves into the escalating tensions, succinctly highlighting the fears on both sides, and examines how the resolution of this debate could influence the future of digital interactions.
Encryption transforms data into a format that can only be interpreted by authorized users. Its applications encompass:
messaging applications
cloud storage solutions
online banking services
digital wallet systems
web browsing activities
medical data protection
government communications
Strong encryption safeguards:
individual privacy
corporate confidentiality
financial operations
national security frameworks
critical infrastructure
It is a protective shield against cyber threats, ensuring user safety from fraud, data breaches, and unlawful surveillance. Any relaxation of encryption measures creates substantial vulnerabilities that could affect both individuals and economies as a whole.
Governments contend that while encryption serves vital privacy functions, it also offers a cover for illicit activities. Their concerns encompass:
investigative measures regarding terrorism
cases of child abuse
organized cybercriminality
international financial fraud
encrypted communications amongst criminal entities
Authorities argue that these platforms afford criminals an avenue to evade law enforcement, leading to demands for:
access keys
surveillance mechanisms
backdoor accesses
“exceptional access” for official inquiries
Without such tools, they argue, law enforcement capabilities cannot match the evolving digital threats.
While tech companies recognize the importance of safety, they resist creating systems that allow for “selective access.” Their core stance is: A vulnerability for one is a vulnerability for all.
The existence of any entrance for unauthorized entities would lead to:
exploitation by hackers
potential foreign government access
facilitated surveillance
a breakdown in user confidence
increased complexity due to conflicting international laws
Tech companies assert that ensuring comprehensive privacy for every user necessitates uncompromised encryption, as even slight relaxations pose catastrophic risks.
At its core, the encryption debate revolves around a pivotal question:
Who should control users’ private data — the individual, the service provider, or the government?
Tech providers advocate for user autonomy.
Governments push for regulatory oversight.
Users find themselves in a dilemma, uncertain of where to place their trust.
Both sides are wary of relinquishing too much authority to the other.
A series of global events has escalated the urgency in the encryption debate.
Numerous nations have initiated or reinstated legislation mandating:
proof of decryption capabilities
user-side scanning of encrypted content
stricter data retention laws
mandatory compliance from messaging applications
criminal sanctions for non-compliance
These initiatives often originate following significant criminal incidents where encrypted information could not be accessed.
An increasing number of services are adopting end-to-end encryption by default. Applications related to messaging, personal email, online storage, and even social networking are consistently strengthening their encryption standards. As encryption becomes more pervasive, government intervention pressures escalate.
Recently, many firms have strengthened:
default encryption settings
protection for metadata
encrypted data backups
encryption for calls and video communications
hardware-level security measures
These advancements further restrict the visibility that governments intend to preserve.
As nations impose varying encryption standards, tech companies with global operations encounter:
discrepancies in regulations
requirements for local data storage
pressure to comply with requests from foreign authorities
threats of penalties or operational bans
Navigating global business while adhering to conflicting legal frameworks has intensified the ongoing struggle.
Though a backdoor may seem like a straightforward “government-only” key, encryption architecture is inherently complex. Introducing any vulnerabilities could compromise the entire system.
Security specialists warn that backdoors:
can be reverse engineered easily
increase the potential for attacks
erode public trust
cannot be limited to only “good actors”
create inconsistency in global encryption standards
Historical trends indicate that vulnerabilities are rapidly exploited once made available.
Encryption is often viewed as a privacy matter, but it fundamentally supports international commerce. Risks affecting businesses include:
jeopardized financial transactions
corporate espionage incidents
exposure of proprietary technologies
cloud service vulnerabilities
risks to supply chain integrity
dangers to remote working communications
Compromised encryption poses threats not only to digital commerce but also affects overall economic stability, as businesses rely on certainty— any erosion of encryption creates unpredictable risks.
For average individuals, weakened encryption could affect:
online banking processes
medical confidentiality
identity safeguarding
cloud storage security
personal documentation
private communications
Users often use encryption without awareness. Any breaches expose them to various risks, including:
fraud incidents
identity theft occurrences
blackmail threats
surveillance
cyberstalking
financial impacts
These stakes are not abstract but fundamentally human and pressing.
Governments maintain that privacy exceptions are already existing in various legal frameworks. For instance:
warrants are needed for physical searches
financial documents are subject to subpoena
communication metadata can be retrieved
They argue that encrypted platforms should not provide a sanctuary for serious wrongdoers. However, tech companies counter that digital access is inherently different because:
the scope is larger
the risk spans globally
exploitation is easily accomplished
breaches yield severe consequences
This contention culminates in a standoff between absolute security and the necessity of investigations.
Some experts are pursuing new frameworks to circumvent the deadlock, albeit without consensus.
Potential solutions feature:
escrowed encryption keys
device-level inspections
privacy-centric crime detection
judicial access pathways
decentralized encryption management
However, each avenue presents substantial concerns around feasibility, security, and ethical implications.
For tech companies, user trust is essential to their sustainability. If people perceive systems as compromised:
user adoption decreases
income streams suffer
competitors gain ground
economic markets destabilize
Conversely, governments require public confidence to uphold security protocols.
Failing to address digital perils could lead to widespread disillusionment among citizens.
Each party apprehends that their reputations are on the line.
Analysts largely anticipate that the encryption strife will escalate.
Key expectations are as follows:
an increase in governmental demands for monitoring tools
tech companies amplifying default encryption procedures
greater fragmentation of global regulations
more intense public discourse on these matters
crucial court precedents shaping future directions
emergence of new technologies altering the dynamics
This matter is not transient—it’s evolving into a central dilemma of our digital epoch.
The encryption discourse juxtaposes two legitimate priorities: public safety against individual liberties. Authorities seek instruments to combat crime and terrorism, while tech companies maintain that compromised encryption endangers everyone.
This contention isn’t about choosing one faction over another but rather discovering a middle ground that upholds both security and individual freedom. If both sides remain steadfast in their positions, the world is at a decisive juncture.
The decisions made in the near future will directly affect the safety of our digital experiences—impacting banking, personal communications, documentation, and identities. Encryption transcends technicalities; it underpins modern trust, and the urgency of this debate is only set to escalate.
This article offers general insights into the ongoing international encryption discussions. Regulatory frameworks and technological directives differ across nations. It’s advisable for readers to consult expert legal or cybersecurity advice specific to their regions.

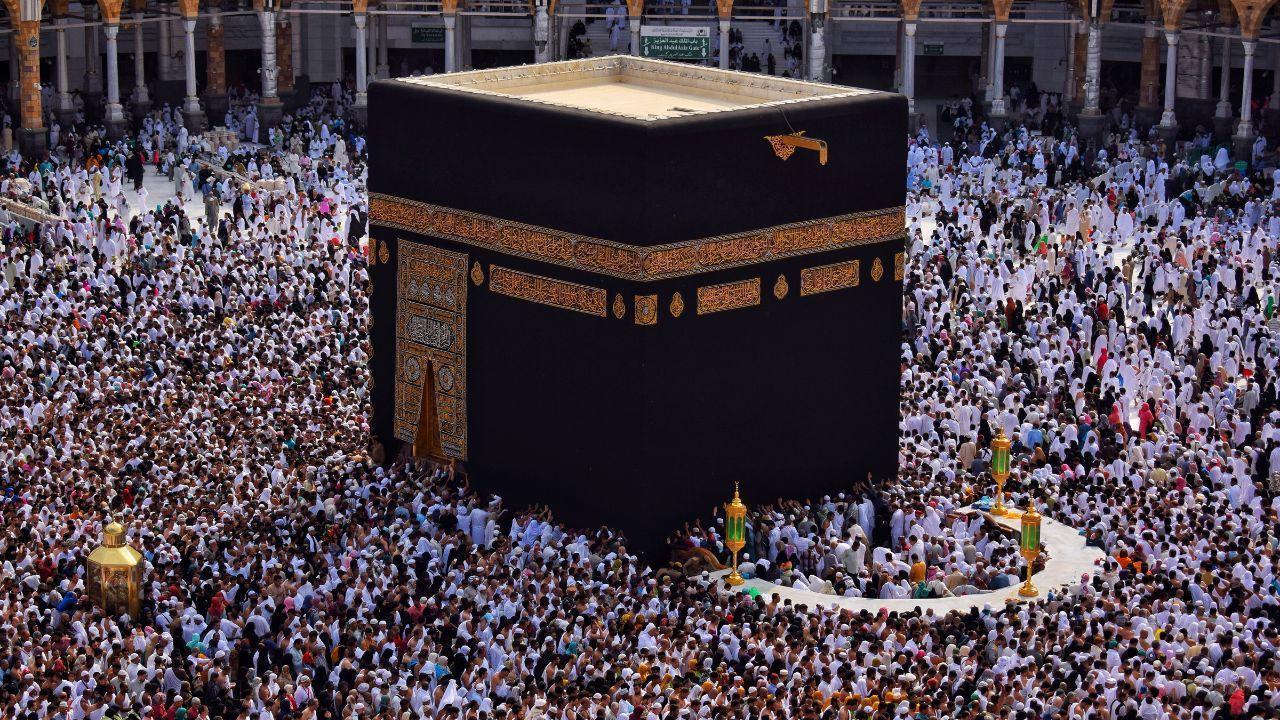







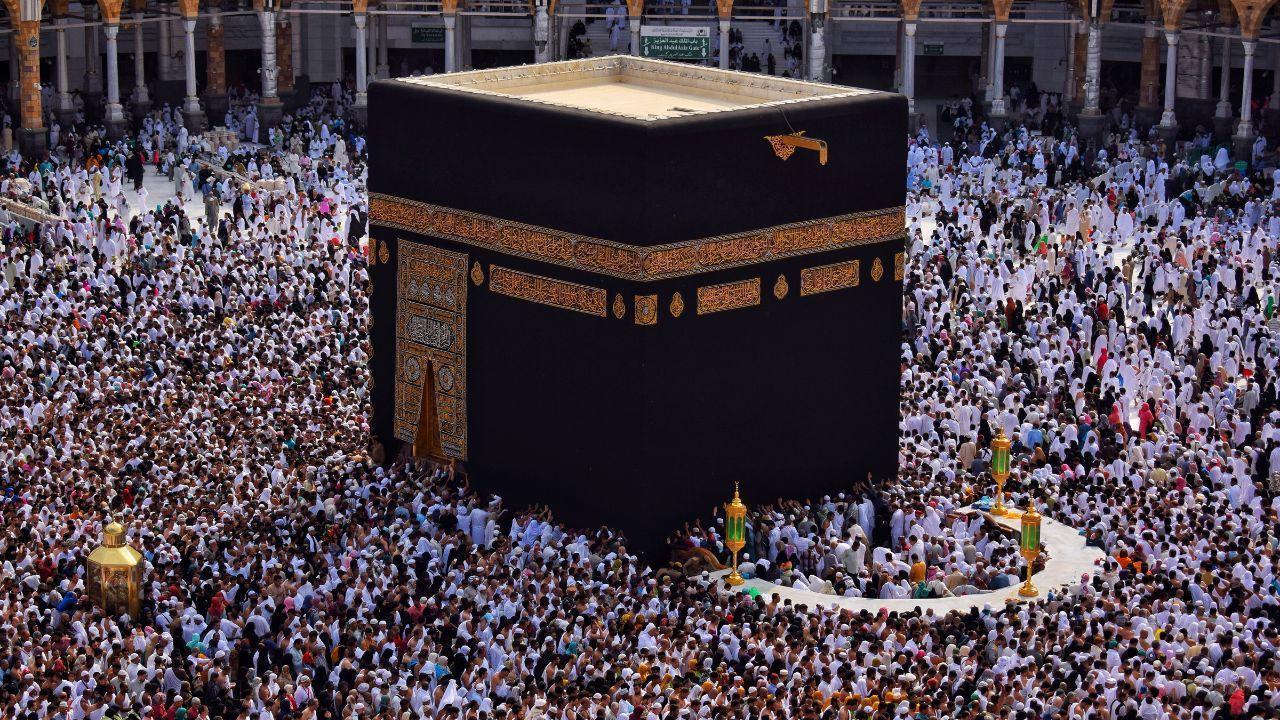
Malaysia, Saudi Boost Haj Cooperation
Malaysia and Saudi Arabia strengthen ties to improve Haj and umrah services, focusing on better mana

Asia Races for Russian Oil Amid Crisis
Asian nations scramble for Russian crude as Iran war disrupts global supply, pushing fuel prices hig

Bella-Saddiq Engagement Wins Malaysia
Bella Astillah and Syed Saddiq’s engagement sparks national buzz, symbolising hope, resilience, and

From Politics to Climate Asia’s Key Shifts
From Japan PM backlash to Philippines work-life issues and Southeast Asia haze, key stories highligh

Floods Kill 45 in Afghanistan and Pakistan
Heavy rains trigger floods and landslides across Afghanistan and Pakistan, leaving dozens dead, hund

Selangor Exco Seeks Tough DUI Punishment
After a fatal Klang crash, Selangor exco urges maximum jail and caning for drink-driving to curb ris