You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!
Post by : Samjeet Ariff
Email scams are among the most prevalent and perilous types of online fraud in our digital age. Almost everyone with an email account has encountered a dubious message, whether it claims to be communication from a bank, delivery service, government agency, or even a job offer. While some of these messages may appear harmless at first, many are expertly crafted traps designed by cybercriminals to steal personal information, financial details, or account access.
What makes email scams dangerously effective is their realistic presentation. Contemporary scammers do not send poorly written messages filled with blatant errors. They employ professional-grade designs, replicate logos, create fake websites, and utilize psychological methods to convince users that their messages are sincere.
Grasping how these scams operate—and the ways to shield yourself—has never been more vital in a time when nearly every facet of our lives intertwines with digital communication.
At the heart of most email scams lies a tactic known as phishing. This occurs when perpetrators masquerade as trustworthy entities to coax users into revealing sensitive data.
These deceptive emails often purport to be from:
The messages frequently generate a sense of urgency, often stating that your account has been locked, a payment has failed, or immediate action is required to avoid repercussions.
The objective is straightforward: compel you to act hastily without exercising caution.
When a user clicks on a link or inputs personal information on a fraudulent site, that data is sent straight to the scammer. This could include passwords, credit card numbers, identity details, or even complete account access.
The primary factor contributing to the effectiveness of email scams is their increasing sophistication.
Scammers now utilize:
Many times, even seasoned users find it challenging to distinguish between legitimate emails and counterfeits.
Moreover, scammers often harvest publicly available information from social media or data breaches to tailor their attacks. For instance, they may use your name, location, or recent online activities to lend authenticity to the email.
This personalization fosters trust and makes individuals more inclined to respond.
Email scams manifest in various forms, yet certain patterns are more prevalent.
A frequently encountered type is the “account verification scam,” where users receive threats of account suspension unless they promptly provide verification information. These emails typically imitate banks or online service providers.
Another common variant is the “payment or invoice scam,” which informs users of fictitious bills or transaction notifications urging them to click links or download files.
Then there are “prize or lottery scams” stating you’ve won cash, gifts, or rewards, necessitating personal details or minor payments to collect.
Business email compromise scams aim at corporations by masquerading as executives or managers pushing for urgent fund transfers.
Each of these scams leans heavily on urgency, fear, or excitement to manipulate decisions.
Even as scams grow more sophisticated, there remain significant flags that can aid in their identification.
Many scams attempt to create pressure with phrases like “act now” or “your account will be terminated.” This psychological maneuver aims to prevent you from making informed decisions.
An unusual sender address is another telltale sign. Even if the display name appears familiar, the actual email address may contain odd characters or misspellings.
Poor grammar or awkward phrasing may also hint at a scam, although contemporary schemes have become increasingly polished.
Suspicious links pose yet another major red flag. Frequently, the displayed text of a link looks credible, but the actual URL leads to an entirely different site.
Attachments from unknown sources warrant caution, particularly if they solicit donwloads of files such as PDFs or executable programs.
Hackers do not solely depend on technical jargon—they employ psychological strategies as well.
One of their most effective tools is fear. Emails that assert “your account has been compromised” or “suspicious activity detected” can incite panic, prompting users to react quickly without verifying.
Urgency is another tactic. Messages that state “respond within 24 hours” or “immediate action needed” inhibit thoughtful decision-making.
Some scams leverage curiosity or excitement, offering fake job opportunities or investment offers promising high returns. Others adopt an authoritative tone, posing as trusted organizations.
Ultimately, the aim is to bypass rational deliberation and push users into unwarranted action.
Clicking on malicious links or providing sensitive information can yield dire ramifications.
Hackers might gain access to:
This may result in financial losses, identity theft, or subsequent scams targeted at your contacts.
In some instances, compromised accounts are exploited to dispatch scam emails to others, furthering the attack's reach.
A single misstep can lead to broader implications beyond the initial victim.
Protecting yourself commences with vigilance and prudent behavior.
A vital practice is to verify emails before acting. Instead of clicking on links directly, it’s safer to manually navigate to the official website of the entity.
Moreover, be cautious of downloading unsolicited attachments, particularly from unknown senders.
Utilizing strong, unique passwords for various accounts can mitigate damage if one account is compromised.
Activating two-factor authentication adds an extra layer of security by necessitating an additional verification step during login.
Regularly updating software and email services can also bolster defenses, as security updates often patch vulnerabilities.
Most crucially, developing a habit of pausing before reacting to urgent messages can dramatically minimize risk.
While technology can thwart numerous threats, human awareness is the most formidable defense against email scams.
Cybercriminals persistently refine their methods, yet their efficacy hinges on human blunders. A cautious, knowledgeable user is markedly more challenging to deceive than someone who reacts impulsively.
Recognizing how scams function enables swift identification of patterns, allowing you to evade common pitfalls.
In today’s interconnected world, awareness is not merely beneficial—it is essential.
Email scams are evolving, but the fundamental strategy remains unchanged: manipulation through urgency, fear, and deception.
By understanding how these scams operate and recognizing the red flags, users can better shield themselves.
Indeed, the goal is not to dread every email, but rather to approach unexpected messages with discerning caution, verify independently, and resist the urge to act impulsively.
In an era where digital correspondence dominates daily life, staying informed is one of the most potent forms of defense.
This article serves for informational and educational purposes only and does not constitute cybersecurity guarantees or expert security counsel. Users should adhere to official cybersecurity protocols and consult professionals for significant security issues.







Malaysia Jobless Rate Stable at 2.9pc
Malaysia’s labour market stayed steady in March 2026 as employment and workforce participation conti
Singapore Woman Jailed After AI Theft Detection
Facial recognition technology at a Singapore supermarket helped identify and arrest a woman accused
Indonesia Faces Measles Surge Amid Vaccine Fear
Misinformation about vaccine side effects spreads across social media as Indonesia records rising me
Indonesia Uses Prison Kitchens for Free Meals
Indonesia plans to involve prisons and inmates in preparing free meals for schoolchildren under a na
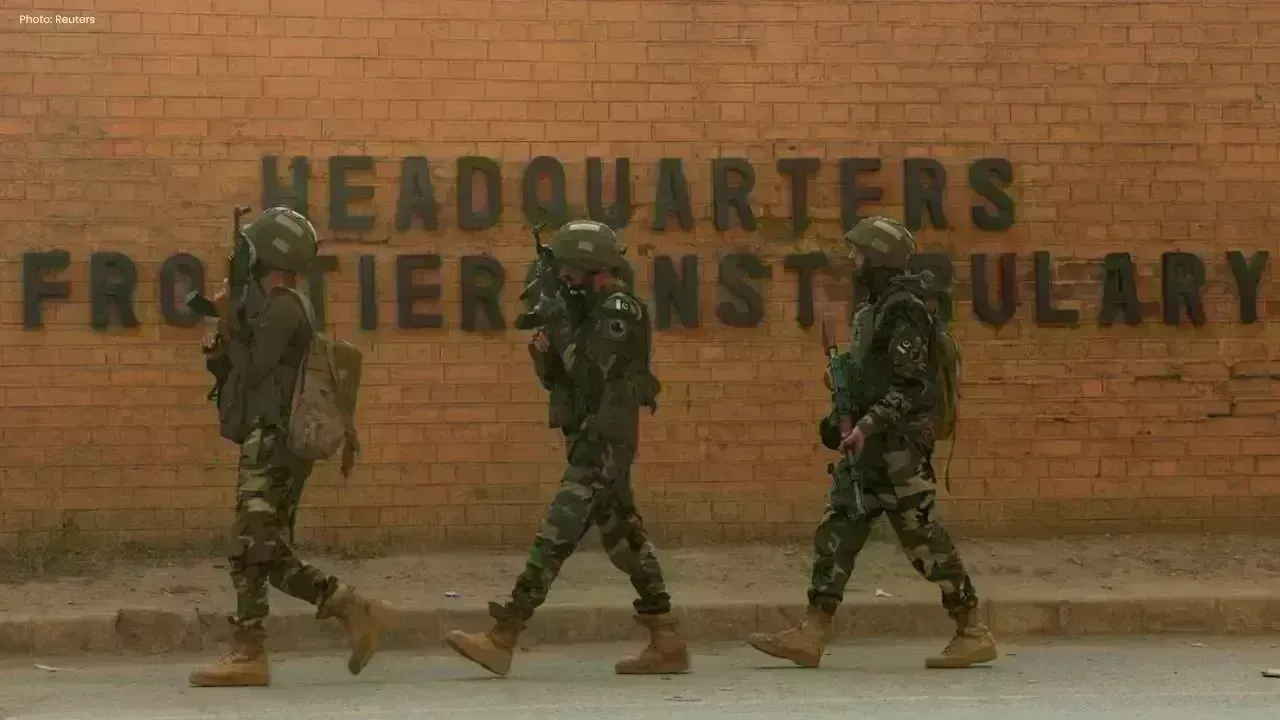
Pakistan Army Chief Issues Fresh Threat to India
Pakistan Army Chief Asim Munir warns of severe consequences in any future conflict while recalling O
173 Indians Held in Sri Lanka Cyber Crackdown
Sri Lankan police arrested 198 foreigners, including 173 Indians, during a major cybercrime operatio