You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
This week brought to light numerous breaches in cloud storage systems across various sectors, triggering significant concern among cybersecurity professionals and companies heavily dependent on these platforms. What began as seemingly random events has unveiled a troubling trend. Various organizations reported unauthorized access, file compromises, unusual downloading patterns, and unexpected shifts in permissions within their cloud environments.
Once marketed as the pinnacle of dependable data management, cloud storage is under increasing scrutiny. As shifting towards cloud-centric operations accelerates, cybercriminals are keenly targeting these platforms as key targets rather than peripheral ones. The rise in remote work, digital operations, and hybrid systems fuels this assault.
These breaches clearly illustrate that attackers are exploiting a diverse range of vulnerabilities rather than simply relying on one method. They capitalize on a mix of predictable misconfigurations, inadequate identity management, and overlooked security vulnerabilities.
This article delves into the specifics of what transpired, the common threads tying these occurrences together, the surge in frequency of these breaches, and strategies for businesses and individuals to safeguard their cloud data moving forward.
As investigators scrutinized the reported incidents, striking parallels were revealed—attackers are capitalizing on foundational vulnerabilities shared across cloud storage systems.
Identified weaknesses include:
misconfigured access permissions
absence or weakness in multi-factor authentication
links that are outdated and still shareable
default settings that are overly permissive
insufficient surveillance of cloud activities
excessive reliance on outdated file-sharing procedures
Such patterns indicate that the failures in cloud security arise not from a lack of technology, but from poor configuration and inadequate oversight.
Cloud platforms are increasingly foundational to businesses globally, providing a central hub for sensitive data like logs, customer details, trade secrets, and backups. This centralization makes them highly attractive to cybercriminals. Factors fueling the rise in attacks this week include:
Data Storage Shift: More data is now maintained on cloud services than on local infrastructures.
Access through Personal Devices: An increasing number of users are engaging with cloud services via personal devices.
Growing Complexity and Misconfigurations: As cloud infrastructures become more intricate, misconfigurations are on the rise.
Automated Vulnerability Scans: Attackers deploy tools that automatically seek publicly accessible storage.
The breaches of this week starkly reveal the ease with which attackers can access valuable cloud data when organizations fail to adhere to basic security practices.
One of the notable patterns from this week was the prevalence of stolen usernames and passwords allowing access to cloud accounts. Attackers gained entry by:
using credential stuffing from leaked passwords
phishing tactics aimed at employees
exploiting easily guessable passwords
gaining entry through shared accounts lacking robust authentication
With cloud services permitting access from any device or location, stolen credentials provide almost instant entry. Without added verification protocols, attackers can manipulate files without detection for prolonged periods.
The increase in incidents tied to credential theft this week highlights the vulnerabilities present in cloud accounts due to ineffective identity protections.
Although multi-factor authentication (MFA) is a critical security layer, this week’s incidents revealed a surprising number of organizations lacking it. In various instances:
administrators neglected to enable MFA
temporary accounts were established without MFA
older accounts retained default settings devoid of MFA
backup accounts were accessible with just passwords
Weak password practices alongside absent MFA transform cloud environments into open gateways for intrusion.
Despite numerous warnings from cybersecurity experts, misconfigured cloud buckets remain a primary cause of breaches. Incidents this week involved:
publically accessible storage buckets
directories lacking authentication
incorrect permissions set during migration processes
broad access allowed for those with links
file-sharing settings that remained exposed long after setup
Such mishaps typically result from human error, leading to knowledge gaps in cloud security principles. Attackers leverage these weaknesses, utilizing automated scans to pinpoint vulnerable buckets.
The speed at which attackers can find misconfigured buckets underscores the need for rigorous configuration reviews.
Another familiar theme this week highlighted attackers capitalizing on old or forgotten sharing links. Organizations often use cloud services to send files to:
contractors
vendors
clients
remote workers
These links typically:
remain perpetually valid
are accessible indefinitely
are spread across emails, messaging apps, or public forums
contain edit or download permissions
Attackers can gain access to sensitive data if they come upon these links—whether deliberately or accidentally—without any need to breach account security.
Several breaches this week stemmed from forgotten share links created months or even years prior.
Some of the incidents this week were not the result of external parties but rather insiders misusing their access to leak vital information. While cloud storage provides convenience for file-sharing, it also raises the risk of:
unauthorized data exfiltration
employees downloading entire folders prior to leaving the company
accidental sharing with unintended recipients
malicious insiders selling confidential data
Cloud environments expand the risk landscape, inviting not just external threats but internal risks as well.
A significant recurring issue this week was the prolonged detection time. Many organizations did not uncover suspicious behaviors until:
unusual download spikes were noticed
employees reported missing files
external partners raised concerns
threat detection systems delivered late alerts
Cloud storage logs are frequently neglected, allowing attackers to operate without detection:
for days
for weeks
or indefinitely
without raising alarms.
Poor monitoring and absence of real-time logging significantly contributed to the depth and scale of the breaches.
Modern cloud setups are intricate. Many organizations utilize:
multiple cloud services
hybrid setups
third-party applications
automated processes
collaborative work environments
Such complexity creates openings for:
misalignment of permissions
inconsistent security protocols
outdated integrations
unauthorized usage of cloud resources (shadow IT)
This week’s breaches frequently originated from such unattended areas, where overlooked services or forgotten integrations provided attackers with an easy entry point.
Attackers are now employing automated technologies rather than conducting manual searches for vulnerabilities. They can:
scan cloud buckets
test widely used passwords
scrape metadata
uncover misconfigurations
detect open ports
This automation expedites the pace of cloud-based attacks. The clusters of breaches observed this week indicate that attackers may be engaging in systematic scanning operations that identify vulnerabilities across numerous organizations simultaneously.
The noticeable surge in cloud storage breaches this week points toward deeper issues businesses must address.
Organizations mistakenly believe that cloud services come inherently secure. They don’t; active security measures are essential.
Weak passwords, careless link sharing, and inconsistent access habits significantly contribute to breaches.
Most breaches are linked to configuration mistakes, which routine training could easily mitigate.
Cloud environments are in constant flux, just like threats.
Many incidents this week arose from basic security settings that went unchecked.
Companies must proactively reassess their cloud implementations to avoid being reactive.
Cloud storage has become integral to daily life. Whether for personal documents, photographs, or work files, users must enhance their security habits to ensure protection.
This measure adds a crucial barrier against credential theft.
Leaked passwords continue to be one of the most significant vectors for attacks.
Delete old links and limit access as much as possible.
Cloud services track device access. Unfamiliar devices can signal compromise.
Should a breach occur, encrypted files remain unreadable.
Certain information is better kept offline.
Not all platforms guarantee the same level of protection.
For businesses, cloud security must be both systematic and ongoing.
One unprotected account could jeopardize the entire network.
Many breaches can be prevented through periodic audits.
Trusting users or devices blindly is not an option.
Real-time oversight can substantially decrease detection timelines.
Stale credentials are pathways for easy entry.
Each integration increases potential vulnerabilities.
Human error remains a leading cause of breaches.
This week's incidents in cloud storage breaches reveal a notable pattern: attackers are increasingly leveraging predictable vulnerabilities that organizations and individuals overlook. Misconfigurations, weak identity controls, careless sharing practices, irrelevant permissions, and lack of monitoring contribute to the susceptibility of cloud environments.
Cloud breaches are seldom due to flaws inherent in the platforms. They arise from how these systems are set up, accessed, and managed. As organizations expand their operations digitally and individuals store significant parts of their lives online, it’s crucial to adopt more consistent and robust cloud security practices.
The patterns identified this week serve as urgent warnings, urging immediate action before incidents escalate further.
This article provides a general overview of evolving trends in cloud security. Security protocols may differ based on provider, region, and organization. Readers are encouraged to consult cybersecurity professionals for tailored advice.

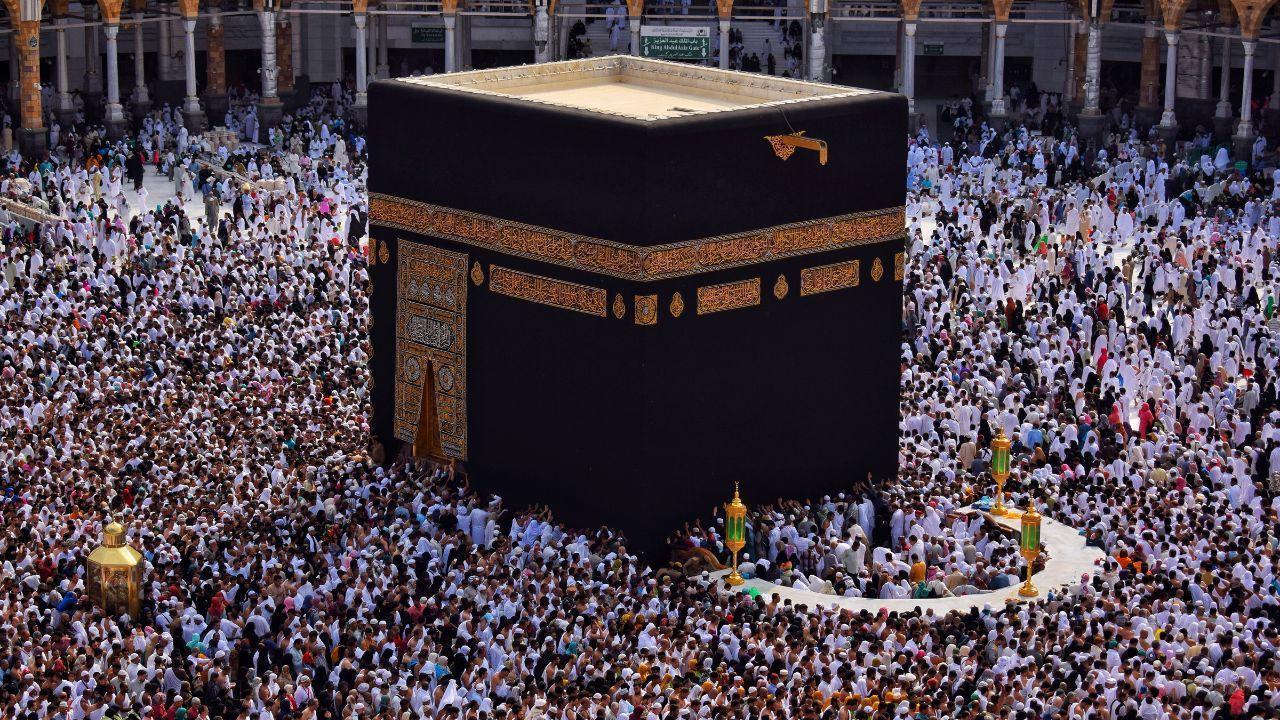







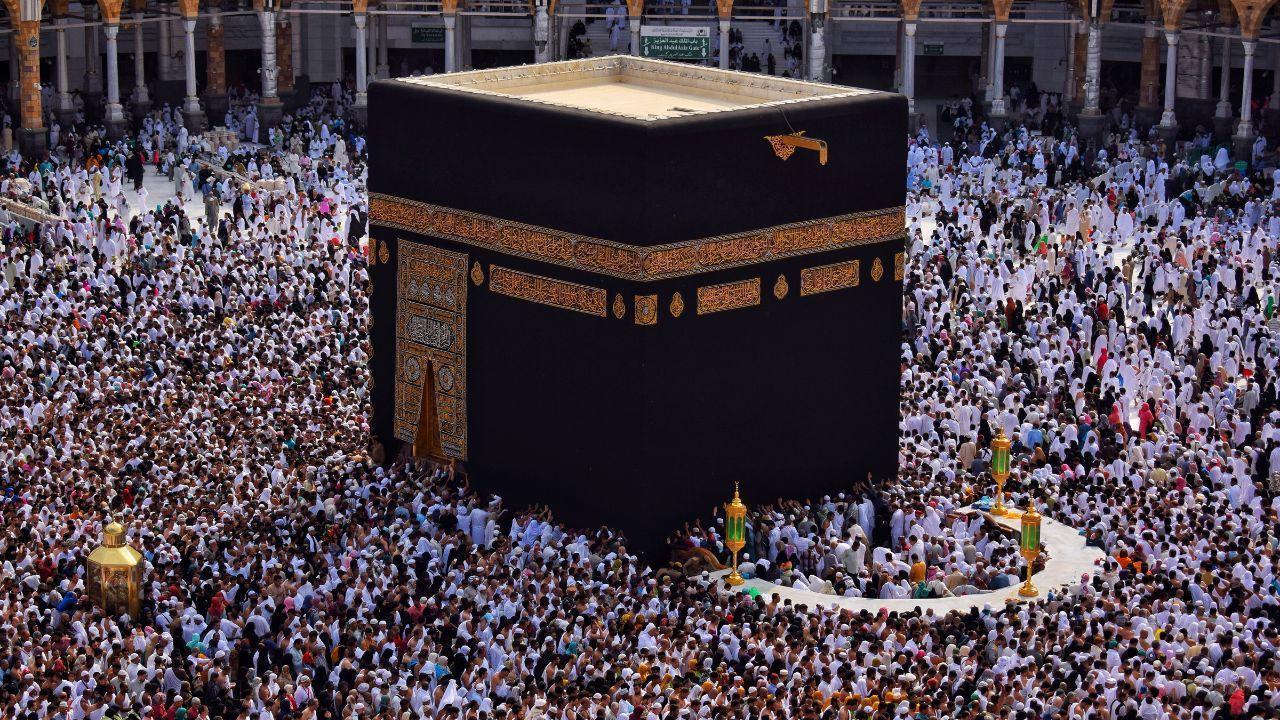
Malaysia, Saudi Boost Haj Cooperation
Malaysia and Saudi Arabia strengthen ties to improve Haj and umrah services, focusing on better mana

Asia Races for Russian Oil Amid Crisis
Asian nations scramble for Russian crude as Iran war disrupts global supply, pushing fuel prices hig

Bella-Saddiq Engagement Wins Malaysia
Bella Astillah and Syed Saddiq’s engagement sparks national buzz, symbolising hope, resilience, and

From Politics to Climate Asia’s Key Shifts
From Japan PM backlash to Philippines work-life issues and Southeast Asia haze, key stories highligh

Floods Kill 45 in Afghanistan and Pakistan
Heavy rains trigger floods and landslides across Afghanistan and Pakistan, leaving dozens dead, hund

Selangor Exco Seeks Tough DUI Punishment
After a fatal Klang crash, Selangor exco urges maximum jail and caning for drink-driving to curb ris