You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
The dark web has traditionally hosted illicit markets offering stolen data, digital assets, and illegal services. However, new findings from cybersecurity analysts and underground interactions indicate a significant evolution: dark web data markets are maturing in complexity and variety. Listings are diversifying, categories are expanding, and sellers are adapting to shifting digital behaviors.
Beyond credit card numbers and leaked passwords, a nuanced marketplace has developed, mirroring changing patterns in how individuals engage with digital platforms and manage personal information. This transformation not only sheds light on the ingenuity of cybercriminals but also underscores emerging vulnerabilities in the management of sensitive data by consumers and enterprises alike.
This article delves into the motivations behind these market changes, the new types of data available, the increasing automation in underground sales, economic influences, and crucial insights for consumers and businesses to bolster protection against emerging threats.
Previously, dark web marketplaces showcased predictable offerings like credit card dumps and forged documents. Now, a wider variety of data types is available, reflecting contemporary digital behaviors.
Recently identified categories include:
behavioral data profiles
advanced device fingerprints
cloud-storage tokens
cryptocurrency exchange logins
personal health records
biometric data traces
ride-hailing account information
digital wallet backups
This variety corresponds with consumers' increasing reliance on interconnected digital services. Cybercriminals are keenly aware of how to exploit possible vulnerabilities at every point in this chain.
A marked trend in new listings highlights the importance placed on "verified" and "current" data. Sellers are marketing:
recently obtained login details
validated financial accounts showing active balances
updated identity credentials
confirmed device-related information
tested cloud access tokens
Sellers are increasingly providing proof, such as partial screenshots or session IDs, to validate the quality of their data. This trend indicates a consumer-like demand among buyers who want reliable and effective data. Sellers who maintain higher standards become reputable, allowing them to command premium pricing.
Adopting a more commercial approach, dark web markets are now offering subscription services. Many sellers provide:
monthly data packages from breaches
ongoing access to updated login lists
regular dumps from compromised devices
weekly harvested data from cloud drives
subscription entry to exclusive data repositories
This shift illustrates a market structure resembling legitimate e-commerce, with criminals recognizing the benefits of consistent revenue and customer loyalty.
Historically, data sold on these marketplaces primarily focused on individuals. Current listings indicate a noted rise in corporate data, including:
internal company emails
digital infrastructure layouts
VPN credentials
access to cloud management tools
human resources records
payroll information
supplier contract details
internal communication records
These data are typically accessed through:
phishing schemes
compromised employee devices
vulnerable cloud services
data harvested from internal tools
credential stuffing utilizing leaked credentials
With enterprises becoming an attractive target due to the profit potential of such data, a single compromised account can lead to extensive sensitive information that is highly marketable.
One of the most pronounced shifts is the growing demand for behavioral data profiles, which encompass:
browsing behaviors
app interaction statistics
location tracking data
purchasing habits
device engagement metrics
Such data is notably valuable as it enables cybercriminals to:
tailor phishing scams to individuals
mimic user behavior for authentication bypass
predict user activities
commit advertising fraud
Behavioral patterns are advantageous due to their longevity in usefulness, often being exploited long after the initial theft.
Session tokens are vital for modern device access, making token-related data particularly appealing to cybercriminals.
Current listings highlight:
stolen cloud synchronization tokens
cookies from high-profile services
tokenized identities from financial apps
authentication strings connected to devices
Tokens can offer privileged access without triggering alerts, representing a shift towards discreet, efficient attacks.
While direct extraction of biometrics like fingerprints is limited, sellers are now offering related data types, such as:
device calibration files for facial recognition
voiceprint models
iris-pattern metadata
behavioral biometric analyses
Though these data cannot typically unlock devices outright, they can facilitate identity theft and fraud. Their appearance signifies an interest in forthcoming authentication technologies.
The surge in cryptocurrency-related data listings includes:
seed phrases
exchange logins
wallet backup documents
transaction history dumps
mining dashboard access
verification paperwork
As the crypto landscape evolves, criminals are recognizing opportunities to exploit users lacking security awareness for their digital resources.
A significant change in these markets is the adoption of automation. Sellers now utilize:
bots for immediate data delivery
automated scraping methods
self-updating inventory systems
dashboards designed like legitimate online stores
integrated messaging solutions
auto-validation processes to verify data accuracy
Automation enhances transaction efficiency:
faster transactions
higher accuracy
greater scalability
increased buyer appeal
For sellers, this reduces interaction risks with clients.
Trust, essential in the dark web, is strengthened through:
rating systems
customer feedback
refund policies
dispute resolution services
This maturity reflects an economy where reliability leads to increased profitability. Highly-rated sellers command higher prices for similar data types.
Related services are also proliferating, including:
wallet conversion services
account monetization facilitators
money mule recruitment
crypto laundering brokers
cash-out services
These services assist individuals in converting stolen assets into cash, indicating a more organized cybercrime network.
The lifecycle of dark web markets includes continual shifts. As older sites face shutdowns, new platforms emerge, providing:
enhanced security
quicker load times
modern interfaces
encrypted communication
sturdier anonymity measures
This ongoing cycle keeps law enforcement in a constant challenge mode.
The shifting landscape of dark web data markets carries significant implications for everyone, from average users to large corporations.
A broader range of data provides more opportunities for diverse attacks.
More corporate data suggests a heightened interest in exploiting internal systems.
Such forms of data can evade conventional security measures.
Increased accessibility boosts the number of active attackers.
Data breaches on one platform can compromise associated services.
Individuals must adopt stronger habits to safeguard their data:
Utilize distinct passwords for each platform
Activate multi-factor authentication whenever feasible
Refrain from storing sensitive data in unencrypted cloud services
Regularly check active sessions and remove devices
Be wary of third-party applications that seek extensive permissions
Monitor financial accounts for unauthorized activity
Avoid unnecessary sharing of personal documents online
Organizations should fortify their identity and access management protocols:
The evolution of dark web data marketplaces highlights broader global cybersecurity challenges. As digital networks grow, adversaries continually refine their methods to acquire, enhance, and profit from unauthorized data. This progression is increasingly rapid, propelled by automation, diversified data types, and the growing demand for high-value stolen information.
Recognizing these trends is vital for both individuals and organizations. Data protection now extends beyond mere password and credit card safeguarding; the dark web has begun to trade in layers of identity, behavioral archives, cloud tokens, and interconnected profile details — emphasizing the need for cybersecurity practices to evolve parallel with emerging threats.
This article offers insights into cybercrime trends based on observed behaviors. It does not name specific perpetrators or active inquiries. Readers should seek expertise from cybersecurity professionals for tailored advice.

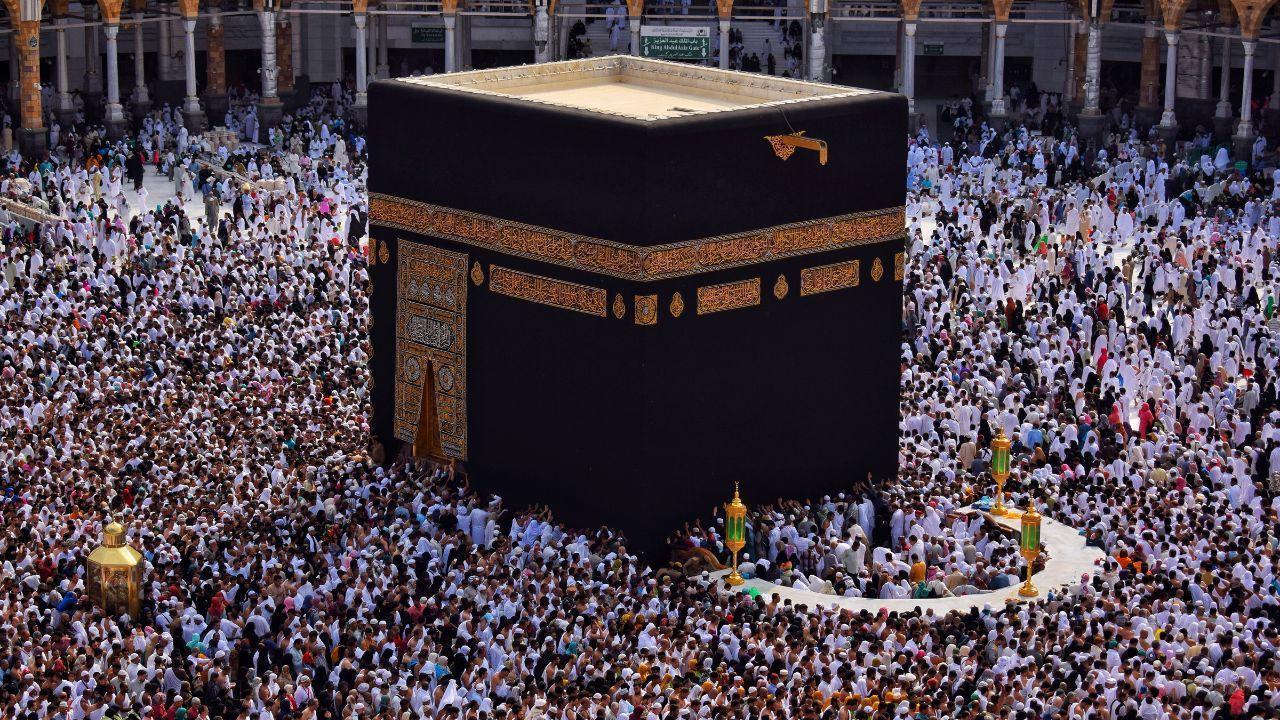







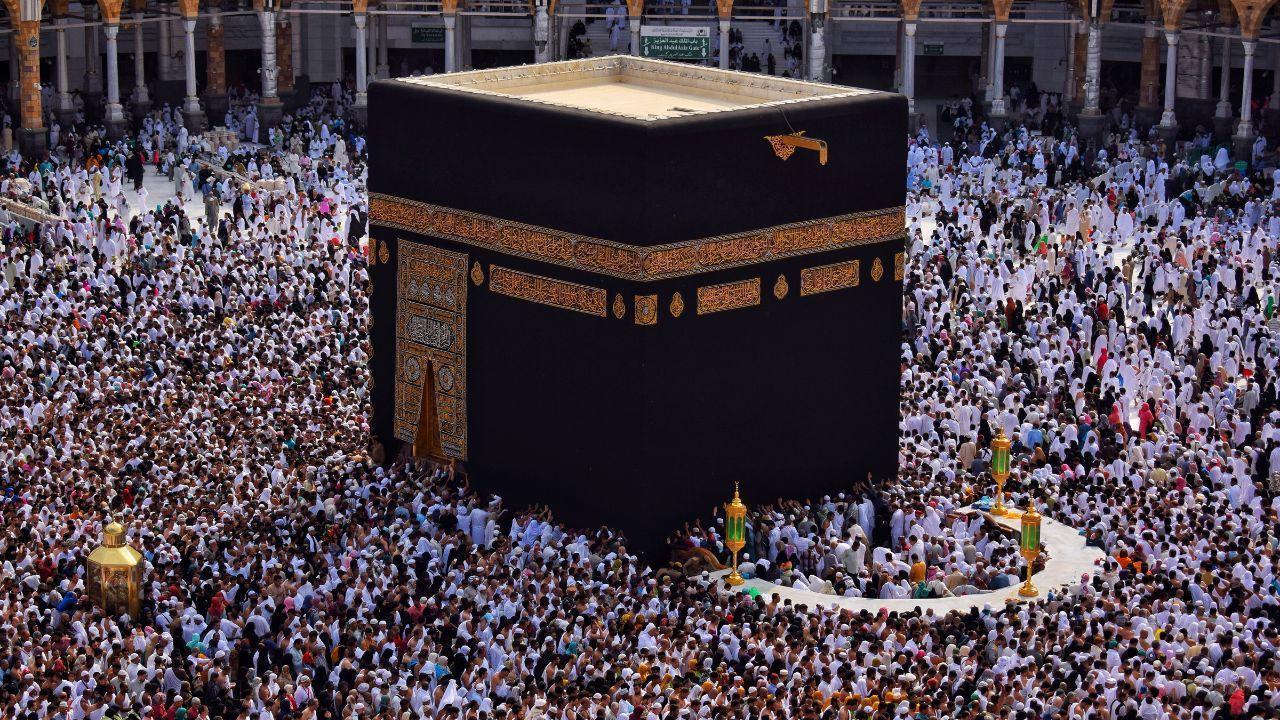
Malaysia, Saudi Boost Haj Cooperation
Malaysia and Saudi Arabia strengthen ties to improve Haj and umrah services, focusing on better mana

Asia Races for Russian Oil Amid Crisis
Asian nations scramble for Russian crude as Iran war disrupts global supply, pushing fuel prices hig

Bella-Saddiq Engagement Wins Malaysia
Bella Astillah and Syed Saddiq’s engagement sparks national buzz, symbolising hope, resilience, and

From Politics to Climate Asia’s Key Shifts
From Japan PM backlash to Philippines work-life issues and Southeast Asia haze, key stories highligh

Floods Kill 45 in Afghanistan and Pakistan
Heavy rains trigger floods and landslides across Afghanistan and Pakistan, leaving dozens dead, hund

Selangor Exco Seeks Tough DUI Punishment
After a fatal Klang crash, Selangor exco urges maximum jail and caning for drink-driving to curb ris