You have not yet added any article to your bookmarks!

Join 10k+ people to get notified about new posts, news and tips.
Do not worry we don't spam!

Post by : Anis Farhan
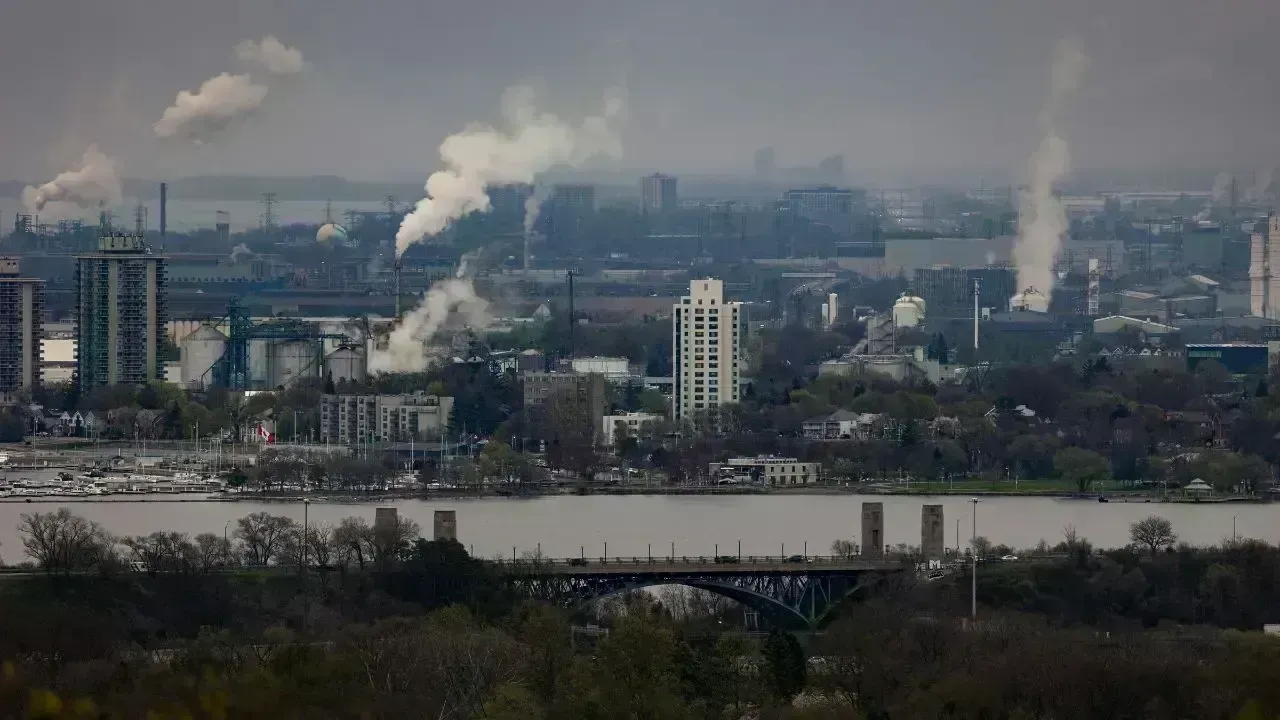
Critical infrastructure — the power grids, water systems, transport hubs, pipelines and communications networks that keep societies running — has become a primary target for cyber attackers. When these systems fail, the consequences are immediate: hospitals lose power, commuters are stranded, communities face water contamination, and economies stall. Recent incidents around the world make one thing clear: cyber threats are no longer hypothetical. They are recurring, adaptive and often interconnected with physical events. Understanding what went wrong, why it mattered, and how to fix it is essential for anyone who depends on modern infrastructure — which is to say, everyone.
Critical infrastructure refers to systems and assets so vital that their disruption would have a debilitating effect on national security, economic stability or public health. This includes energy, water, transport, healthcare, finance and telecommunications. Several traits make these systems attractive to attackers:
They often combine legacy operational technology (OT) with modern information technology (IT), creating wide attack surfaces.
Many control systems were designed for availability and safety, not for hostile threat environments.
Interconnections and third-party dependencies mean a breach in one supplier can cascade across sectors.
Operational continuity pressures can make operators reluctant to take systems offline for patches or upgrades.
These vulnerabilities are not theoretical. Recent breaches have exploited simple lapses — weak credentials, outdated software, and unprotected remote access — and turned them into large-scale disruptions.
In September 2025 a cyber incident disrupted automated check-in systems across major European airports, forcing staff to revert to manual processes and causing flight delays and cancellations. Investigations pointed to a third-party provider’s systems being compromised, illustrating how a fault in one supplier can ripple through an entire transport network. The event also occurred alongside drone incursions in parts of Europe, highlighting how cyber and physical threats may be blended to magnify disruption.
Lesson: transportation operators must map third-party dependencies, enforce strict supply-chain security controls, and plan manual fallback procedures so operations can continue safely when automated systems fail.
The 2021 Colonial Pipeline ransomware attack remains a textbook example of how cybercriminals can force an operator to suspend operations to contain a breach. The attackers gained initial access through compromised credentials and used ransomware to encrypt key systems — and while billing systems were cited as the trigger for the shutdown, the ripple effects were real and immediate: fuel shortages and price spikes. The incident underlined the strategic risk posed by ransomware against single-point operators.
Lesson: energy operators must assume ransomware is a systemic threat. Preventive measures (network segmentation, identity hygiene, multi-factor authentication) and recovery planning (isolated backups, tested failover) are business-critical.
The attack on a U.S. water treatment facility where an attacker briefly altered chemical dosing to dangerously high levels demonstrated how a compromised control interface can directly threaten human safety. Even when the incident was quickly corrected, it exposed the risks inherent in remote access and poorly monitored supervisory systems. Federal advisories have repeatedly flagged SCADA and remote management systems as high-risk points that require stricter controls. CISA+1
Lesson: utilities must treat OT access as a safety-critical issue. Least-privilege access, continuous monitoring, and stringent vendor controls are minimum requirements.
Large-scale events in Ukraine (and subsequent campaigns) showed that well-resourced persistent threat actors can disrupt electricity distribution by targeting both IT and OT layers. Attacks that once aimed to steal data evolved into tools to disable breakers, manipulate control logic and erase forensic trails. These campaigns were not merely criminal — they were strategic, timed and intended to create outages and fear.
Lesson: power system defenders must adopt an adversary-centric outlook. That means not only patching vulnerabilities but anticipating tactics used by advanced attackers and investing in resilient grid architectures.
Across sectors and geographies, successful attacks tend to exploit a small set of recurring weaknesses:
Weak or reused credentials and missing multi-factor authentication. Attackers frequently leverage stolen credentials obtained via phishing or purchased on criminal markets.
Unsegmented networks. Flat networks allow lateral movement from an IT compromise into sensitive OT environments.
Outdated and unsupported software. Legacy controllers and management consoles are often unpatched or run obsolete OS versions.
Third-party and supply-chain exposure. Service providers and vendors with network access become pivot points into larger ecosystems.
Lack of tested incident response and business continuity. Many operators lacked realistic playbooks and backups that were offline, untampered and readily recoverable.
Fixing these core issues reduces risk across the board. The tasks are organizational as much as technical.
Security planning must accept that breaches will occur. That means designing systems to contain compromise, maintain critical functions and recover quickly. Implement strict network segmentation between IT and OT; apply microsegmentation where possible; and ensure critical control systems can run in manual or degraded modes safely.
Credential hygiene is non-negotiable. Enforce strong passwords, multi-factor authentication, frequent rotation of privileged accounts and use of privileged access management tools. Where remote maintenance is necessary, require just-in-time access, session recording and approval workflows.
Catalog and continuously assess all third-party providers with network or data access. Contractual requirements should enforce minimum security baselines, incident notification timelines, and the right to audit. Consider zero-trust network access for vendors rather than VPNs that grant broad network reach.
Maintain an up-to-date inventory of assets, including legacy controllers. Prioritize patching for internet-facing controllers and management consoles, and isolate unsupported devices while plans for replacement or compensating controls are executed.
Traditional IT security tools miss many OT anomalies. Deploy monitoring tailored to industrial protocols, use anomaly detection that understands normal operational patterns, and integrate OT alerts into the central Security Operations Center (SOC) with runbooks specific to industrial incidents.
Create joint IT-OT incident response plans, run regular tabletop and live exercises, and rehearse recovery steps including safe manual operation. Verify the integrity and accessibility of offline backups and practice restoring operations under time pressure.
Train staff at all levels on phishing, social engineering and safety protocols. Empower frontline operators to report anomalies without fear of punishment, and build cross-functional teams that include engineering, IT, communications and legal for rapid decision making.
Recent events have reinforced that government action is necessary to raise baseline defenses. Key policy levers include:
Minimum critical-infrastructure security standards. Governments can mandate resilience controls — identity management, inventory, segmentation and incident reporting — tailored to sector risk.
Information sharing and threat intelligence. Public-private sharing hubs allow rapid distribution of indicators, tactics and mitigations. Timely intelligence narrows the attacker’s window of advantage.
Support for smaller operators. Many attacks hit smaller utilities and co-ops that lack large security budgets. Grants, shared SOC services, or cooperative purchasing can elevate defenses across the whole sector.
Legal frameworks for supply-chain accountability. Rules that require vendors to meet security standards and disclose breaches in a timeline help reduce hidden systemic risk.
Policy must be flexible and outcome-focused: prescriptive lists become obsolete fast, but outcome requirements (e.g., demonstrable segmentation, logged privileged access) maintain relevance.
Ransomware and operational losses have forced insurers to reassess cyber risk. Premiums rise, coverage narrows, and underwriters demand demonstrable controls. That creates a virtuous cycle when operators invest in basics — insurers reward improved posture — but it also risks leaving critical players uninsured. Public programs or backstops might be needed to prevent systemic financial exposure in sectors where a single outage can cascade widely.
Investors and boards must treat cyber resilience as an operational KPI, not just an IT cost center. The reputational and regulatory fallout from a failure can far exceed direct remediation expenses.
While the basics remain critical, defenders must also track emerging trends that change the threat landscape:
Supply-chain attacks on managed service providers continue to be a preferred vector.
Hybrid threats that combine physical disruption (drones, sabotage) with cyber operations can multiply impact.
AI-assisted reconnaissance makes targeted phishing and vulnerability discovery faster for attackers; defenders should use similar tools to prioritize risks.
OT malware sophistication continues to improve — some adversaries now tailor tools to specific control hardware.
Regulatory fragmentation across regions and countries complicates multinational operators’ compliance efforts.
Keeping ahead requires continuous learning, investment in R&D, and cross-sector cooperation.
Protecting critical infrastructure is a societal task, not only an operator’s burden. Citizens and local organizations can:
Support and pressure local utilities and authorities to publish resilience plans and community recovery steps.
Be vigilant about scams that target employees or the public during crises (phishing campaigns spike during outages).
Build local preparedness — households and businesses that can ride out short outages reduce systemic panic and demand surges.
A resilient community reduces the human harm when technology fails.
Several responses have shown best practices in action: operators that avoided panic, used tested manual procedures, engaged regulators early and communicated transparently to the public limited damage and rebuilt trust faster. Investment in redundant controls and offline backups paid off repeatedly. These real-world recoveries are proof that deliberate preparation — not merely advanced tools — is the decisive advantage.
Immediate (0–12 months): Patch critical exposures, enforce MFA, map third-party access, and run incident response drills.
Short term (1–2 years): Deploy OT-aware monitoring, implement network segmentation, and establish threat-sharing relationships.
Medium term (2–4 years): Replace unsupported devices, automate recovery testing, and pursue zero-trust architectures for vendor access.
Long term (4–5+ years): Build domestic manufacturing and secure supply chains for critical control components and invest in workforce training to expand OT cybersecurity expertise.
Progress will require funding, political will and cross-sector cooperation — but the cost of inaction is higher.
Recent attacks on airports, pipelines, water systems and power grids provide a clear syllabus for improvement: lock down access, segment networks, scrutinize suppliers, monitor OT environments, and practice recovery. Technology will continue to evolve, and attackers will adapt — but organizations that build resilient systems and disciplined processes will reduce risk and maintain public trust. In critical infrastructure, failure is not only operational; it can be existential for communities. The lesson is simple: prepare deliberately, invest wisely, and treat cyber resilience as essential infrastructure in its own right.
This article is for informational purposes only. It summarizes observed trends and publicly reported incidents to draw practical lessons for operators, policymakers and communities. It does not offer legal, technical or financial advice. Readers should consult sector specialists and official sources for operational decisions.







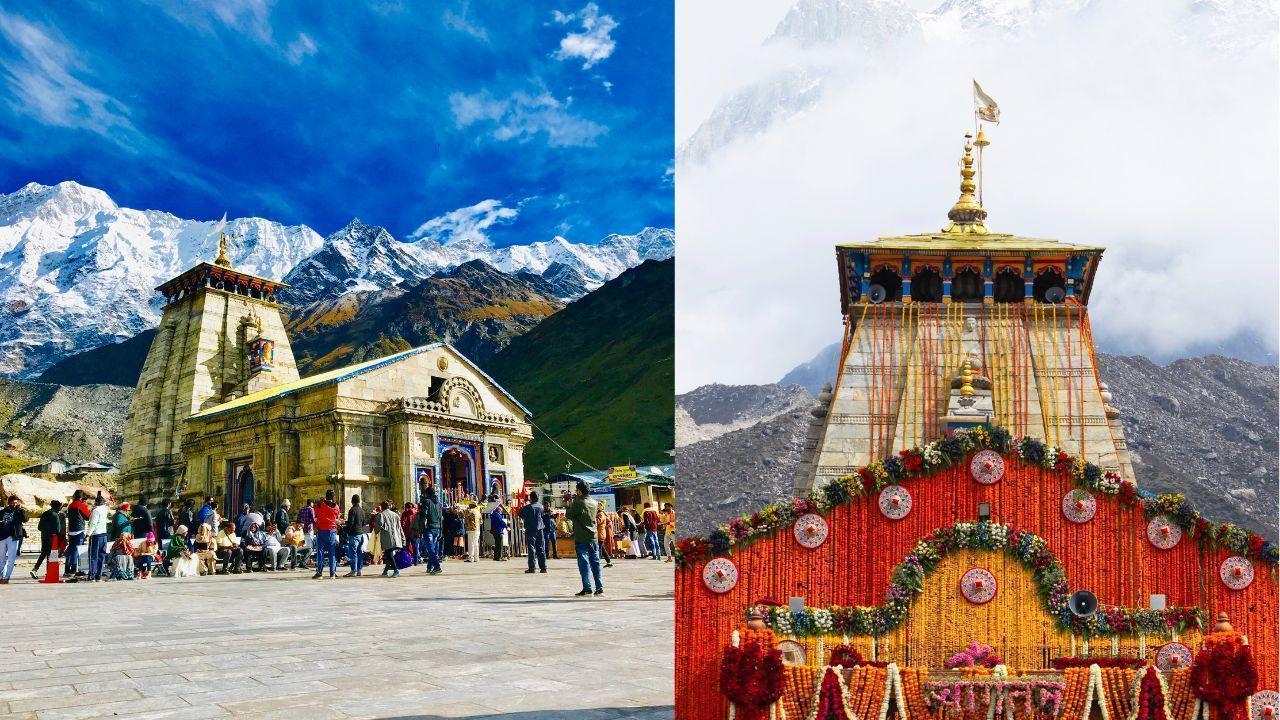
Kedarnath Temple Opens for Yatra 2026
Sacred shrine reopens after winter as Char Dham Yatra begins with rituals, chants, and thousands of
Pope Visit Puts Prison Abuses in Focus
Pope Leo XIV visits Equatorial Guinea prison highlighting rights concerns and migrant deportation is

Taiwan President Delays Africa Visit Move
Lai Ching-te postpones Eswatini trip after flight permits revoked, Taiwan accuses China of pressurin

Elevate Your Career: 7 Free Online Courses Available in 2026
Discover 7 free online courses to enhance your skills and career prospects without financial strain.
Vietnam Clarifies Local Env Inspection Powers
Authorities confirm commune level officials can inspect businesses for environmental compliance unde

Vietnam Issues Rules on Tech Forensic Exams
New circular sets standards for forensic experts and regulates examination processes in science and